Lemmy
Everything about Lemmy; bugs, gripes, praises, and advocacy.
For discussion about the lemmy.ml instance, go to !meta@lemmy.ml.
Do another one, replace the last panels "alpha Lemmy app" to "password manager" lol
How many password managers have you been trying out this week?
Sorry, but that's literally every online service. For example if you buy a new virtual server it takes like 5 minutes till a Chinese IP starts to try root passwords.
If someone actually wanted to harm Lemmy they'd just DDOS the biggest instances for a month (which would be easy, it's mostly single servers after all) or attack it with so much spam and large images that storage would break.
We need moderation tools
Here's hoping Sync and Boost lead the way
Here's hoping Sync and Boost lead the way
Or better yet, let's hope Free Software apps lead the way and ditch the proprietary ones.
Well, Sync and Boost were well established already. It's probably gonna take some time for the new foss ones to catch up
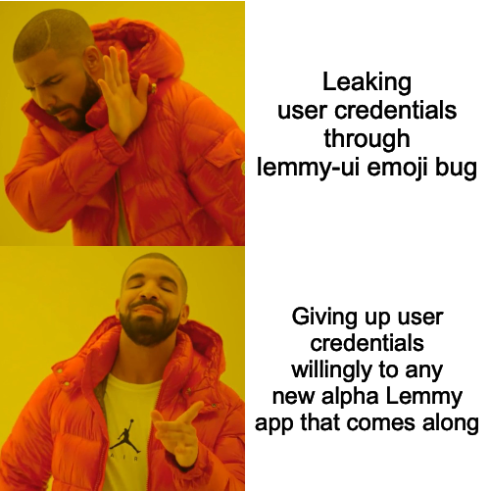
Feels like this will be a very common occurrence with people rushing to build and use new apps, and host new servers. There are plenty of positives to fediverse vs centralized, but it doesn’t come without negatives.
Oauth2 login support for apps would certainly be very welcome.
I am using the Liftoff app. It looks pretty safe but I don't really know.
It's open source and pretty popular (for a Lemmy app at least) so it should be pretty safe
Indeed, this is a real weak spot with Lemmy's security. I honestly think we need to place more emphasis on implementing OAuth2, when I have the time I'll have to take a look at that again to see if I'm able to.
Using open source apps, especially with more than one contributor, is currently the best option to be safe from this kind of attack.
It helps, but it's still not a silver bullet. For example, a Lemmy app could contain no malicious code in its open source repository, but malicious code could still be added to a binary release in an app store.
Yeah, downloading from fdroid or izzyondroid kinda solves that.
Izzy directly sends over the APKs from GitHub releases. F-Droid does their own builds which is partly why they're so slow to update.
That's why F-Droid is the safest Android app repository. If I'm not mistaken, every app they offer is rebuilt from the public source code by the repo package maintainer.
OSS does not guarantee security, ever. Please let's not fall into false sense of security.I
But in this case, if an app is open source, there is a higher chance of discovering that it sends your credentials somewhere else than in closed source app
That assumes people are looking at that and know what they're doing and aren't malicious actors. None of this is guaranteed. Famous examples of major OSS security vulnerabilities have already shown this.
1password is probably the most valuable subscription I pay for.
If anyone's looking for a free and open source option, Bitwarden is also great.
You two have no idea do you? lol
When you pass your password into an app, it can just copy and store it. If at any point you put a password through, even once, its compromised and no password manager will help in the slightest.
I make bobApp, you download bobApp, if you put a password into it, you are done.
edit: answering both of you.
Then i misunderstood. After i typed this I noticed others said what you meant. My bad.
You're correct, but by maintaining distinct passwords with a password manager you make sure only the one account is compromised. 2FA also helps, you may have the username and password, but the 2FA code that you were given needs to be used immediately or else it will expire, and an expired 2FA code won't allow you to successfully breach the account you're trying to break into to.
KeePassXC is free and completely offline
And if you want it to be online, you can just share your .kdbx file between your computers using Syncthing or whatever.
Are there any known apps that should be avoided? I’m using Mlem and Memmy.
It's not about any specific app.
They are just using many words to say 'remember logging in on these apps means giving them your full username/password.'
We really need a better way to log in from 3rd parties. It'd be nice if we could crowd fund features, I'd def pay up for some sort of app-password system or other
Not yet, this post is just a warning that it might happen
Not sure about the other apps, but Memmy keeps your password stored in the app. But generally speaking I don’t think Gavin is a malicious person. He spent 3 weeks with beta tests before he was even comfortable pushing it to Apple App Store and the code is reviewed by Apple before being included to watch for malicious scripting. I am not saying people don’t get malicious scripts passed through Apple, but from what I have seen of Gavin’s work, he doesn’t seem the type that would do that.