After lots of testing I found a configuration that works for me! In the end it is very simple, but I am quite a newbie at this so it took some effort to figure out what works. ChatGPT helped a bit too - and also confused me a lot - but it helped.
What I do now is:
I set up a wireguard tunnel. The VPS in this example has the 'wireguard' ip of 10.222.0.1, and my home network is 10.222.0.2. These are my configs (/etc/wireguard/wg0.conf):
VPS wireguard config:
spoiler
[Interface]
Address = 10.222.0.1/24
ListenPort = 51820
PrivateKey = <VPS Private key>
[Peer]
PublicKey = <Home network public key>
AllowedIPs = 10.222.0.2/32
PersistentKeepalive = 25
Home network (Respberry pi) config :
spoiler
[Interface]
Address = 10.222.0.2/32
PrivateKey = <Home network private key>
[Peer]
PublicKey = <VPS Public Key>
Endpoint = <VPS_IP>:51820
AllowedIPs = 10.222.0.0/16
PersistentKeepalive = 25
Then, I use the following iptables commands in the VPS to map requests to port 80 and 443 to the ports 80 and 443 of the tunnel. What really confused me for a while was that I did not know that I needed to include the "POSTROUTING" step so that the packets get sent back the correct way, and that I had to set net.ipv4.ip_forward=1 in /etc/sysctl.conf:
IP tables in VPS:
spoiler
iptables -t nat -A PREROUTING -p tcp --dport 443 -j DNAT --to-destination 10.222.0.2:443
iptables -t nat -A POSTROUTING -p tcp -d 10.222.0.2 --dport 443 -j SNAT --to-source 10.222.0.1
iptables -t nat -A PREROUTING -p tcp --dport 80 -j DNAT --to-destination 10.222.0.2:80
iptables -t nat -A POSTROUTING -p tcp -d 10.222.0.2 --dport 80 -j SNAT --to-source 10.222.0.1
Then, in my home network I use the standard nginx config:
spoiler
server {
server_name website.com;
listen 80;
location / {
return 301 https://$host$request_uri;
}
}
server {
server_name website.com;
listen 443;
location / {
proxy_set_header Host $host;
proxy_pass http://0.0.0.0:<Website Port>;
}
# certificate management here
ssl_certificate /etc/letsencrypt/live/website.com/fullchain.pem; # managed by Certbot
ssl_certificate_key /etc/letsencrypt/live/website.com/privkey.pem; # managed by Certbot
include /etc/letsencrypt/options-ssl-nginx.conf; # managed by Certbot
ssl_dhparam /etc/letsencrypt/ssl-dhparams.pem; # managed by Certbot
}
This configuration seems to work, and since both ports 80 and 433 are mapped you can use certbot to generate and renew the SSL certificates automatically.
I am still learning, and this is the first thing that worked - so there might be a better way! But a lot of things I tried would not complete the SSL handshake correctly. > push m

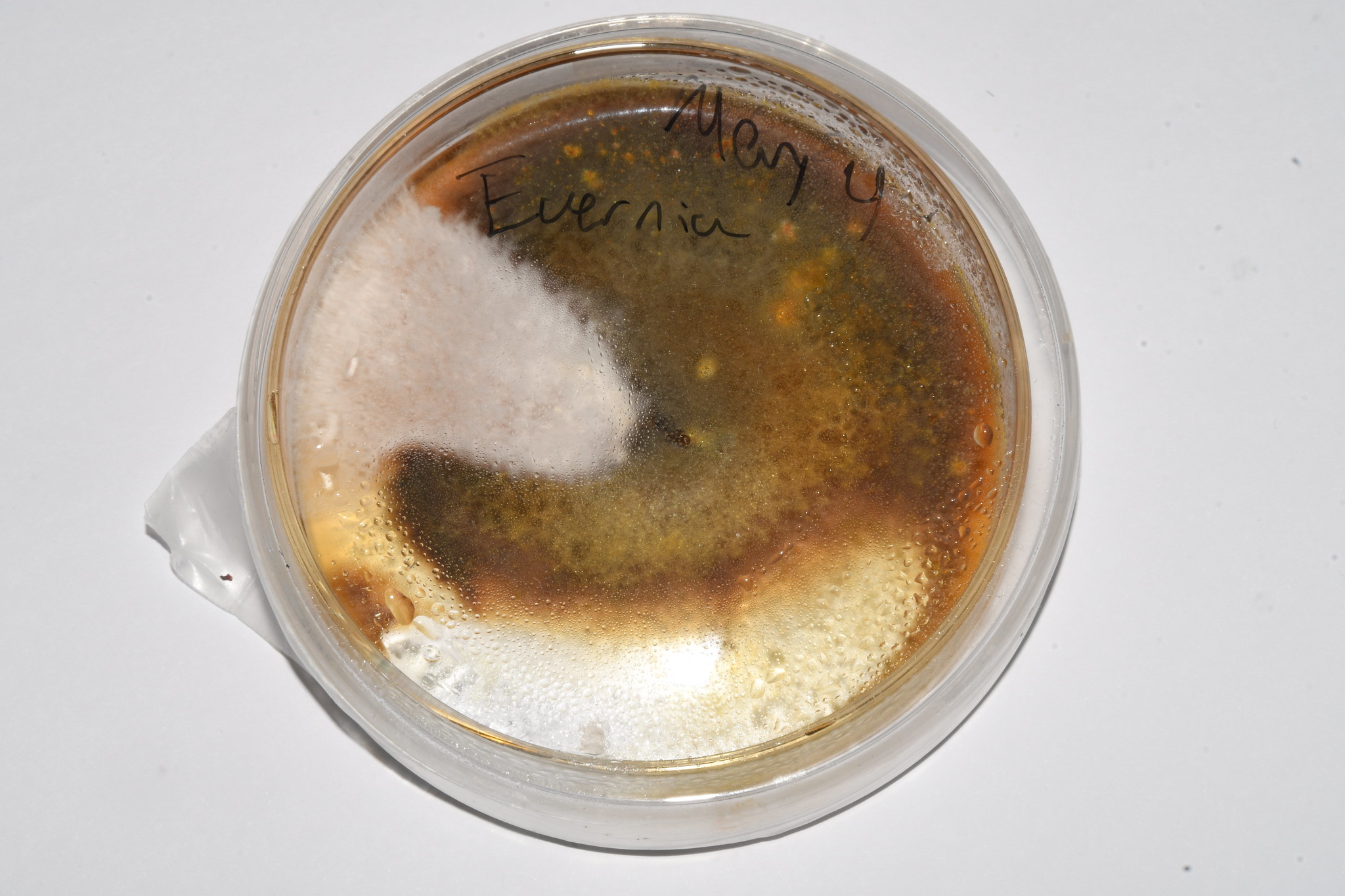

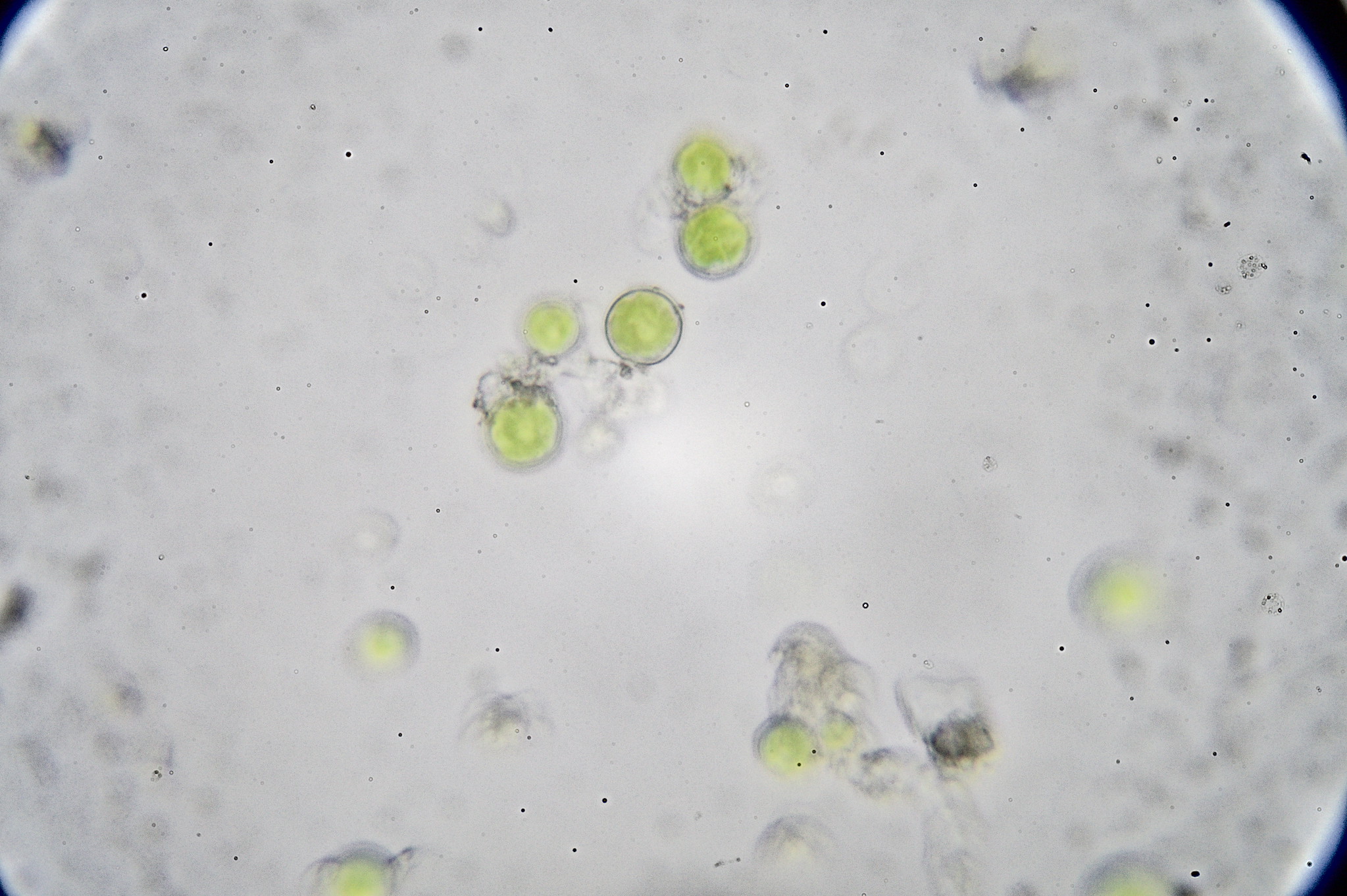

So, how is the situation with the white spots? Did they end up being benign?